Imagine you wake up to find a suspicious PancakeSwap trade executed from your wallet: a token you never approved has been swapped, a balance vanished, and you need to know what happened before calling support or moving funds. For a BNB Chain user in the US, the immediate actions are observational and analytical: trace the transaction, inspect the smart contract involved, and evaluate whether the token or the swap was a benign mistake, a failed trade, or an exploit. This article walks through that decision path while comparing the analytic tools, trade-offs, and verification practices that matter most on BNB Chain today.
The goal is practical: give you a reproducible heuristic for triage (what to check first and why), a comparison of the PancakeSwap-focused trackers versus general explorer features, and a clear sense of what verification actually proves — and where it leaves uncertainty. The piece emphasizes mechanism (how explorers expose blockchain data), limitations (what logs and verified source code do not guarantee), and useful rules of thumb you can apply immediately.

Start with the concrete triage: transaction hash, nonce, and receipts
The single most immediate artifact after an unexpected event is the transaction hash (a 66-character TX hash). Use it to confirm block inclusion, UTC timestamp, sender and recipient addresses, and the transaction status (success/failed). Two short checks cut through ambiguity: (1) the nonce field on the transaction tells you whether the transaction fits the sender’s expected sequence — mismatched nonces often indicate replay or scripting errors; (2) the receipt and internal transactions tabs reveal whether a contract call created internal transfers (token movements between contracts) rather than a plain wallet-to-wallet transfer.
These fields are mechanical facts recorded by the chain; they cannot lie. But they also do not interpret intent. A success status means the transaction ran to completion under Ethereum Virtual Machine rules — not that it was safe. Internal transaction visibility helps when a swap routes through multiple contracts (typical on DEXs like PancakeSwap), so you can see which contract actually moved tokens and whether a router contract was used.
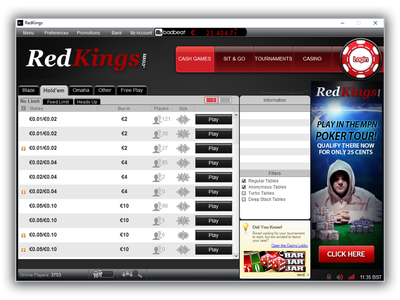
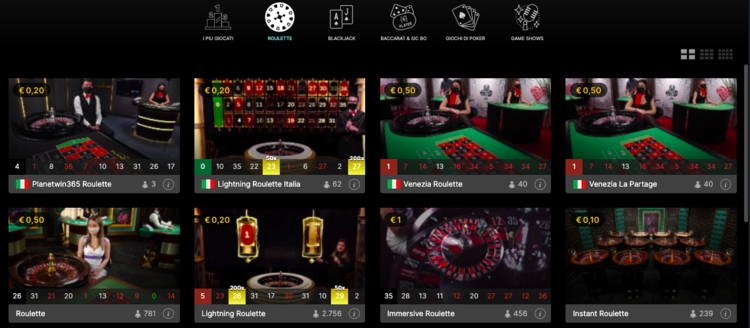
Comparing PancakeSwap trackers and general chain explorers
PancakeSwap trackers (third-party dashboards or integrated DEX pages) give domain-specific summaries: liquidity pool health, price impact for a hypothetical trade, slippage history, and top LP holders. They make some things easier: for a potential rug pull or liquidity drain, a PancakeSwap tracker shows pool reserves and recent removes quickly. But general explorers — the canonical, on-chain record and feature set — provide deeper forensic tools: event logs, verified source code access (Code Reader), burn tracking, gas analytics, and MEV builder data. Each has a role; using them in tandem is often the fastest way to a reliable conclusion.
Trade-offs to weigh: PancakeSwap trackers are faster for DEX-focused signals but rely on correct indexation and sometimes offer aggregated metrics that obscure low-level details. Explorers give raw evidence but require some literacy: reading event logs, understanding topics, and interpreting internal transactions needs practice. For forensic work after an unexpected swap, start with the tracker to see pool movement and then pivot to the explorer to validate the low-level traces and contract code.
If you need the canonical starting point for any of these investigations, a full-featured chain explorer is essential. For BNB Chain users, this platform provides the transaction receipts, event logs, burn statistics, and verified contract code that let you move from suspicion to an evidence-backed assessment. A handy entry is the bnb chain explorer, which links directly to those artifacts and APIs.
What “verified smart contract” actually means — and what it does not
Smart contract verification on explorers is one of the most consequential features for BNB Chain users. When a developer submits source code that matches the on-chain bytecode, the explorer’s Code Reader publishes the human-readable Solidity or Vyper contract. That enables auditing, function mapping, and event decoding. Mechanically, verification confirms that the published source corresponds to the deployed bytecode — it ties readable code to the immutable runtime.
Important limitation: verification proves equivalence between source and bytecode, not the safety of that code. A verified contract can still implement malicious logic (backdoors, owner-only minting, or privileged blacklists). Verification makes malicious intent easier to inspect and detect, but it is not a stamp of approval. For example, verified token contracts often include owner-only functions that can change fees or pause transfers — legal in code, risky in practice.
Practical verification checklist: after finding a suspect contract, open the Code Reader to (1) check for owner or admin roles and whether they can mint tokens or change fees, (2) locate events (Transfer, Approval, and any custom events) and cross-reference them with event logs from the transaction, and (3) search for external calls to known router or LP addresses. If source is unverified, treat the contract as opaque; you can still read ABI-decoded logs if the explorer suggests an inferred interface, but risk remains higher.
MEV, gas analytics, and what to watch for in front-running or sandwich attacks
Explorers with MEV Builder integration surface block construction metadata and sometimes show which transactions were included through builder processes. For users trading on PancakeSwap, that matters because MEV-aware blocks can reduce exposure to certain front-running techniques when builders favor fair sequencing. The concrete signals to watch: unusually high gas prices on nearby blocks, a pattern of sandwiching (a buy then an immediate sale that squeezes price), and spikes in the “gas used vs gas limit” savings metric — which can indicate attempts to overpay for priority.
Gas analytics on BNB Chain are practical beyond cost control: they help infer adversarial behavior. If the gas price for your trade was far below concurrent offers, your transaction may have been left vulnerable in the mempool; conversely, consistently high gas use in the same short block windows could indicate automated bots competing to capture MEV. These are correlations and mechanistic cues, not proof of malicious intent; they should trigger deeper inspection into who benefits in post-trade token distributions.
Token and holder analysis: what token tracking reveals and conceals
Token tracking on a capable explorer shows transfer history, top holders, and contract-initiated moves. For PancakeSwap liquidity tokens and BEP-20 tokens more broadly, the top-holder distribution is a strong signal: a highly concentrated top 3–5 holders combined with visible large liquidity removals is a red flag. However, token-holder snapshots can be misleading when custodial wallets or exchange-managed addresses appear as single holders; public name tags on the explorer help disambiguate known exchange deposit addresses from single-entity ownership.
Another boundary condition: internal transactions (contract-to-contract movements) frequently carry the economic substance of DEX trades, but many casual users only scan standard transfer tabs. For robust analysis, always check internal transactions and event logs to see whether token movements were normal transfers, burns, or contract-executed swaps. The explorer’s burn tracking also supplies a net supply signal — cumulative BNB burned via mechanisms — which can be relevant to long-term tokenomics assessments, but burns alone do not guarantee demand or price support.
Developer APIs and automation: scaling your investigations
If you are building monitoring, alerts, or a wallet integration, the explorer’s JSON-RPC API lets you pull block data, transaction receipts, and event logs programmatically. This is where the trade-off between latency and completeness appears: polling too frequently raises rate-limit and noise issues; polling too slowly may miss short-lived MEV patterns or flash-loan-driven anomalies. A pragmatic compromise is event-driven polling keyed to specific addresses or tokens you care about, combined with a higher-frequency mempool monitor for high-value trades.
For users in the US worried about regulatory or exchange-related investigations, programmatic access also helps produce auditable logs: timestamped receipts, decoded event sequences, and snapshots of token-holder distributions can be exported for compliance or dispute resolution. Keep in mind the API gives access to on-chain facts only; reconstructing off-chain intent or cross-exchange netting still requires external data.
Historical evolution, current state, and near-term signals to watch
BNB Chain analytics evolved from basic block explorers to integrated analytics platforms with MEV data, verified code readers, and burn tracking. The network’s PoSA consensus and growing Layer 2 and storage ecosystem (opBNB, BNB Greenfield) mean explorers now must span multi-layer data and cross-system flows. Today’s explorer gives users visibility into validators, slashing risks, and block rewards — signals that matter for network security assessments and for understanding validator behavior that can affect transaction ordering.
Watch next: adoption of opBNB or other Layer 2 flows will change how liquidity and MEV surface in layer-1 traces. If more volume migrates off-chain, on-chain explorers will need to integrate L2 rollup data to preserve actionable transparency. Signals that change the playing field include systematic differences in burn rates, large shifts in liquidity from L1 pools to L2 pools, or upgrades to contract verification workflows that make immutable provenance easier to assert.
Decision-useful takeaways — a short heuristic you can use now
1) Triage first: check TX hash, nonce, status, and internal transactions. If nonce mismatches or internal transfers are present, prioritize chain evidence over UI summaries. 2) Verify code: if the contract is verified, scan for owner privileges, minting rights, and pause functions. Verified ≠ safe. 3) Cross-check DEX dashboards: use PancakeSwap trackers for pool-level signals, then confirm flow and actors on the explorer. 4) Use gas and MEV signals as risk indicators, not conclusive proof. 5) Automate exports for audits if you rely on logs for disputes or compliance.
These heuristics turn a bewildering raw blockchain record into an efficient decision process, suitable for immediate triage or deeper forensic work. They also respect the limits of what the chain proves: facts of execution are reliable; motives, intent, and off-chain coordination often are not directly visible.
FAQ
Q: If a token contract is verified, can I assume it’s safe to interact with?
A: No. Verification confirms the source matches on-chain bytecode and makes audit easier, but it doesn’t prevent malicious code or owner powers. Always inspect owner roles, mint functions, and emergency controls in the verified source before trusting a token indefinitely.
Q: How can I tell if my PancakeSwap trade was front-run or part of a sandwich attack?
A: Look for adjacent transactions in the same block: a higher-fee buy before your trade and a sell immediately after benefiting the same address is a classic sandwich pattern. Gas price spikes and MEV builder metadata can support this inference. These are mechanistic indicators rather than definitive proof, so combine them with token flows and recipient analysis.
Q: Are burn statistics meaningful for short-term trading?
A: Burn totals are a medium-to-long-term supply signal. Short-term price moves are usually driven by liquidity shifts, market sentiment, and trading activity. Use burn analytics as part of a multi-factor view, not as a standalone trading signal.
Q: What should I monitor to reduce exposure to MEV?
A: Use higher gas if you need faster inclusion, consider private or relayed transaction submission where available, and watch for exchanges or builders that advertise fair ordering. Yet remember: private relays and builder services trade off transparency for protection; you gain front-running resistance but lose some public audibility of order flow.